May times we all share our phone with our friends and other peoples for many reasons. But, on the other way, we need to protect our privacy and security to the content of our smartphone. If you use Android, doing a quick search on Google Play store, you will find many apps to hide files and folders. Its not a big deal if you have a lot of RAM and storage on your device, but what when its to low? So to now more on the topic, than follow these steps below to hide Folders and files without installing any app.
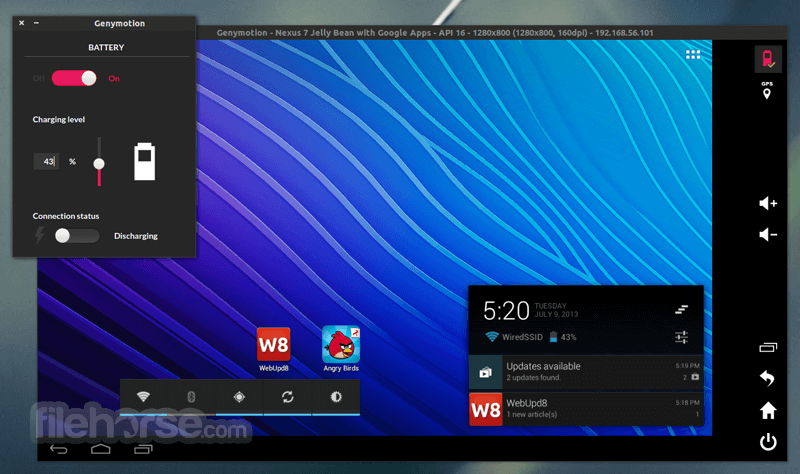
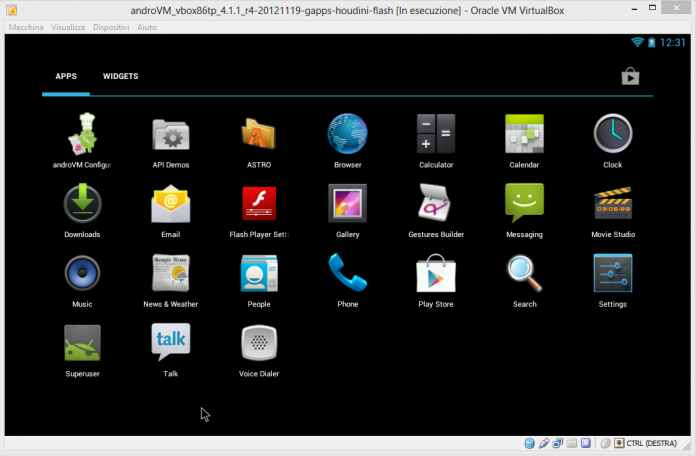
> Check Out: Top 15 Best Android Emulators: Experience Android On PC (2020)
Steps to Hide Files and Folders on Android Without Third Party App
However, if you don’t want to add a new app to hide your data, we have a simple solution. Below in this article, with a simple Trick, i will show you how to hide files and folders on Android OS without the need of installing a third party application.
How To Hide Folders Or Files on Android device
Follow these steps below to hide Folders and files without installing any app.
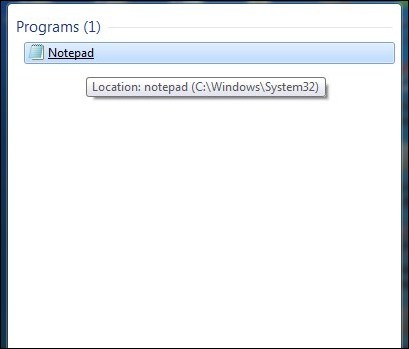
Step #1. Go to File manager or File Explorer. Every Android device comes with a default file manager.
Step #2. Create a new folder and move all your private (data) in it.
Step #3. Now you will need to rename your folder by just adding a dot (.) before the name of your folder. E.g. if your folder name is,New folder rename it to .New folder
Step #4. Doing that your folder will disappear. Don’t need to worry about it because it is just hidden in the phone. You will have full access to it like a normal folder.
Step #5. Now, to see your folder, you will need to unhide it or select show hidden files and folders option. Go to menu option in a file manager and select show hidden folder.
> Read Next: Top 10+ Best WiFi File Transfer Apps For Android (2020)
This is one of the easiest way to hide your private files in a folder without using any third party application in your device. Hope you find this article helpful. If you have any question please let us know in the comment section below, follow us on twitter and facebook for more news and updates.